Trusted by Millions
Save up to 58%*
Get easy-to-use, easy-to-install antivirus protection against advanced online threats. Plus online privacy and ID theft protection with select plans.
Get easy-to-use, easy-to-install antivirus protection against advanced online threats. Plus online privacy and ID theft protection with select plans.
For the first year. Savings compared to the renewal price.
Offer details below.*
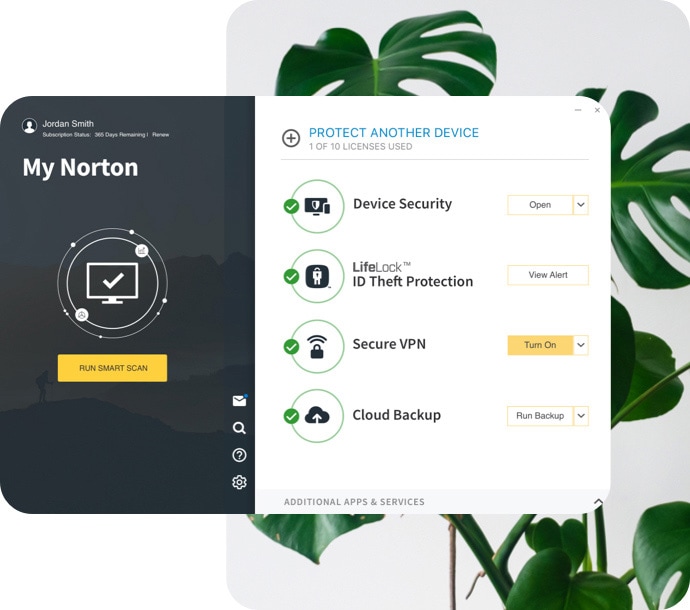
Norton™ 360 with LifeLock™ Plans
Devices + online privacy + identity protection
Help block hackers from your devices, keep your online activity private and protect your identity, all-in-one. It’s never been easier.
Norton™ 360 Plans
Devices + online privacy protection
Device security helps block hackers and Norton Secure VPN helps you keep your online activity private.

Norton™ Secure VPN Plan
Online privacy protection
Norton Secure VPN helps block hackers from seeing what you do online, over public or even home Wi-Fi.

Norton Small Business
Enjoy peace of mind knowing your business’s devices and customer data are more secure.
Norton technology blocks thousands of threats every minute.
Count on decades of experience and a proven track record of keeping people safer every day.
Get the protection you and your family need in one place.

A trademark of Ziff Davis, LLC. Used under
license. Reprinted with permission. © 2022 Ziff
Davis, LLC. All Rights Reserved. Best of the Year
awarded in 2021.

AAA Rating in Consumer Endpoint Protection
from SE Labs, Jan-Dec 2021.

AV-TEST, “Best Protection and Best Performance”
Norton 360, Jan-Dec 2021.
No one can prevent all cybercrime or identity theft.
2 Requires an automatically renewing subscription for a product containing antivirus features. For further terms and conditions please see norton.com/virus-protection-promise.
3 If your plan includes credit reports, scores, and/or credit monitoring features ("Credit Features"), two requirements must be met to receive said features: (i) your identity must be successfully verified with Equifax; and (ii) Equifax must be able to locate your credit file and it must contain sufficient credit history information. IF EITHER OF THE FOREGOING REQUIREMENTS ARE NOT MET YOU WILL NOT RECEIVE CREDIT FEATURES FROM ANY BUREAU. If your plan also includes Credit Features from Experian and/or TransUnion, the above verification process must also be successfully completed with Experian and/or TransUnion, as applicable. If verification is successfully completed with Equifax, but not with Experian and/or TransUnion, as applicable, you will not receive Credit Features from such bureau(s) until the verification process is successfully completed and until then you will only receive Credit Features from Equifax. Any credit monitoring from Experian and TransUnion will take several days to begin after your successful plan enrollment.
4 Only available on Windows systems (but not in S mode or on ARM processors).
5 SafeCam features are only available on Windows (excluding Windows in S mode, Windows running on ARM processor).
8 Video Supervision requires a browser extension on Windows and the in-app Norton Browser on iOS and Android. It monitors videos viewed on YouTube.com (but not YouTube videos embedded in other websites or blogs) and on Hulu.com (but only on Windows). It does not work with the YouTube or Hulu apps.
12 Identity Lock cannot prevent all account takeovers, unauthorized account openings, or stop all credit file inquiries. The credit lock on your TransUnion credit file and the Payday Loan Lock will be unlocked if your subscription is downgraded or canceled.
13 Enables telecommunication and/or wireless carriers to share your personal information with NortonLifeLock so it may deliver the services.
† We do not monitor all transactions at all businesses.
‡ Monitoring available on Windows™ PC, iOS and Android™ devices. Not all features available on all platforms.
§ Monitoring not available in all countries and varies based on region.
¶ Home Title Monitoring feature includes your home, second home, rental home, or other properties where you have an ownership interest.
Ω In your state, the office that maintains real estate records could be known as a county recorder, registrar of deeds, clerk of the court, or some other government agency.
** Service can be used once every 90 days. You acknowledge our ability to submit a deletion request on your behalf depends on the presence of your personal information on the data broker sites we monitor.
The Norton and LifeLock Brands are part of Gen. LifeLock identity theft protection is not available in all countries.
Copyright © 2024 Gen Digital Inc. All rights reserved. Gen trademarks or registered trademarks are property of Gen Digital Inc. or its affiliates. Firefox is a trademark of Mozilla Foundation. Android, Google Chrome, Google Play and the Google Play logo are trademarks of Google, LLC. Mac, iPhone, iPad, Apple and the Apple logo are trademarks of Apple Inc., registered in the U.S. and other countries. App Store is a service mark of Apple Inc. Alexa and all related logos are trademarks of Amazon.com, Inc. or its affiliates. Microsoft and the Window logo are trademarks of Microsoft Corporation in the U.S. and other countries. The Android robot is reproduced or modified from work created and shared by Google and used according to terms described in the Creative Commons 3.0 Attribution License. Other names may be trademarks of their respective owners.